 Tech tips is planned as a regular series, to help small business owners make more efficient use of technology.
Tech tips is planned as a regular series, to help small business owners make more efficient use of technology.
Barely a week goes by without news of a major password breach exposing millions of user names and passwords, with the passwords sometimes posted to the Internet! If you use the same password over and over, or even a variation of it, you’re playing Russian roulette. The only question is when, not if, you’ll be compromised.
The password manager solution
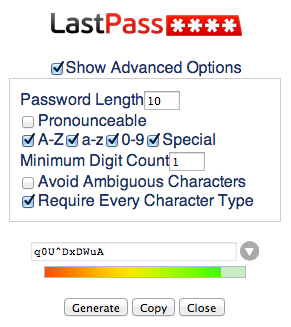
Fortunately there is an easy (and free) solution — a password manager. Create one strong password to access it and from then on you can use gobbledygook like $%kw^*HJ(* for other sites; your password manager will remember them for you.
Make your master password different from any you’ve previously used, and incorporate numbers, letters and special characters. One way to do this is to pick a word (perhaps spelling it backwards), add a significant number (the year you started your business?) and bracket it with the same special characters. The result might look something like #mybiz2011#. Don’t use that one though; make up your own!
LastPass
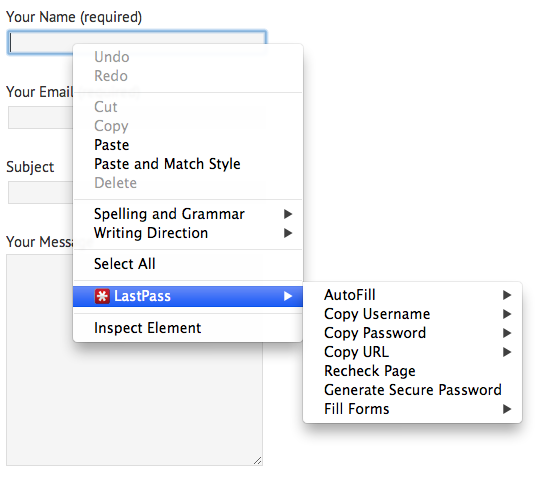
My password manager of choice is LastPass. My passwords are available across all my machines and I can even log into LastPass.com on someone else’s computer and access a password should the need arise. But wait you say, that means these passwords are stored online! How can that be secure? I had the same concerns and it took a two-hour security podcast to convince me. Here are the details if you want to dig into the tech. For something less intense, check out Lifehacker’s article on which password manager is the most secure. FWIW, they say this about LastPass:
Most secure option: LastPass is the leader of the online password managers because it’s both easy to use and can be locked down pretty tightly. LastPass security options allow you to add stronger two-factor authentication, restrict logins by country and enable other features, such as a dedicated security email address and restricted mobile access.
I’m including some screenshots below…
Leave a Reply
You must be logged in to post a comment.